Inside the Intel Ivy Bridge Microarchitecture
Introduction
Contents
The Ivy Bridge microarchitecture will be used in the third-generation Core i3, i5, and i7 CPUs, to be released in 2012. It brings minor modifications to the Sandy Bridge microarchitecture used in the second-generation Core i processors, but with a completely new graphics engine, a PCI Express 3.0 controller, and a new manufacturing process. Let’s see what is new.
For a better understanding of this tutorial, we recommend that you read our “Inside the Intel Sandy Bridge Microarchitecture” tutorial before continuing.
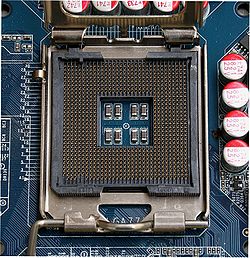
The good news is that CPUs based on the Ivy Bridge microarchitecture will use the same socket as Sandy Bridge processors (socket LGA1155). This means that you will be able to upgrade your second-generation Core i processor to a third-generation Core i model without having to change the motherboard. The Ivy Bridge microarchitecture incorporates a PCI Express 3.0 controller, which doubles the bandwidth of the PCI Express slots connected to the CPU (i.e., the video card slots) from 500 MB/s per lane to 1 GB/s per lane. However, if your current motherboard doesn’t have PCI Express 3.0 channel chips, access to these slots will be limited to 2.0 speeds (500 MB/s per lane).
The Ivy Bridge microarchitecture expands the Sandy Bridge microarchitecture by adding the following new features:
- Socket LGA1155
- PCI Express 3.0 controller, which increases the bandwidth of the PCI Express lanes connected to the CPU from 500 MB/s to 1 GB/s; motherboards must use PCI Express 3.0 channel chips, otherwise, the video card slots will be limited to 2.0 speeds
- Two new security features: a digital random number generator and a Supervisory Mode Execution Protection (SMEP)
- Float16 format conversion instructions, which convert between a 16-bit compressed floating point memory format and a 32-bit single precision format
- Improved performance for instructions that handle strings (REP MOVSB and REP STOSB)
- Four new instructions for allowing applications to access the FS and GS registers of the CPU
- Support for DDR3L (i.e., low-power DDR3) memories in mobile CPUs
- DirectX 11 graphics engine
- New 2D graphics engine
- Support for three video monitors
- Memory overclocking limit was increased from 2,133 MHz to 2,800 MHz, and memory clock can be configured in 200 MHz increments now
- Dynamic overclocking, allowing you to change the clock ratio on unlocked CPUs without needing to reboot the PC, and higher clock ratios (up to 63) available for unlocked CPUs
- Improvements in power management
- 22-nm manufacturing process
Let’s now talk a little more about some of these new features.